CIH (computer virus)
| CIH | |
|---|---|
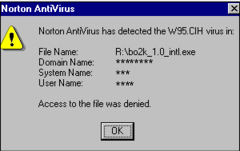 | |
| Antivirus intercept message on a Windows 95 system | |
CIH, also known as Chernobyl or Spacefiller, is a Microsoft Windows 9x computer virus that first emerged in 1998. Its payload is highly destructive to vulnerable systems, overwriting critical information on infected system drives and, in some cases, destroying the system BIOS. The virus was created by Chen Ing-hau (陳盈豪, pinyin: Chén Yíngháo), a student at Tatung University in Taiwan.[1] It was believed to have infected sixty million computers internationally, resulting in an estimated NT$1 billion (US$35,801,231.56) in commercial damages.[1]
Chen claimed to have written the virus as a challenge against bold claims of antiviral efficiency by antivirus software developers.[2] Chen stated that after classmates at Tatung University spread the virus, he apologized to the school and made an antivirus program available for public download. Weng Shi-hao (翁世豪), a student at Tamkang University, co-authored with the antivirus program.[2] Prosecutors in Taiwan could not charge Chen at the time because no victims came forward with a lawsuit.[3] Nevertheless, these events led to new computer crime legislation in Taiwan.[2]
The name "Chernobyl Virus" was coined sometime after the virus was already well known as CIH and refers to the complete coincidence of the payload trigger date in some variants of the virus (actually the virus creation date in 1998, to trigger exactly a year later) and the Chernobyl disaster, which happened in the Soviet Union on April 26, 1986.[4]
The name "Spacefiller" was introduced because most viruses write their code to the end of the infected file, with infected files being detectable because their file size increases. In contrast, CIH looks for gaps in the existing program code, where it then writes its code, preventing an increase in file size; in that way, the virus avoids detection.[4]
History
[edit]The virus first emerged in 1998. In March 1999, several thousand IBM Aptivas shipped with the CIH virus,[5] just one month before the virus would trigger. In July 1999, copies of remote administration tool Back Orifice 2000 given out to DEF CON 7 attendees were discovered by the organizers to have been infected with CIH.[6] On December 31, 1999, Yamaha shipped a software update to their CD-R400 drives that was infected with the virus. In July 1998, a demo version of the first-person shooter game SiN was infected by one of its mirror sites.[7]
CIH's dual payload was delivered for the first time on April 26, 1999, with most of the damage occurring in Asia.[8] CIH filled the first 1024 KB of the host's boot drive with zeros and then attacked certain types of BIOS. Both of these payloads served to render the host computer inoperable, and for most ordinary users, the virus essentially destroyed the PC. Technically, however, it was possible to replace the BIOS chip,[citation needed] and methods for recovering hard disk data emerged later.[citation needed]
Today, CIH is not as widespread as it once was, due to awareness of the threat and the fact that it only affects older Windows 9x (95, 98, ME) operating systems.
The virus made another comeback in 2001 when a variant of the LoveLetter Worm in a VBS file that contained a dropper routine for the CIH virus was circulated around the internet under the guise of a nude picture of Jennifer Lopez.
A modified version of the virus called CIH.1106 was discovered in December 2002, but it is not widespread and only affects Windows 9x-based systems.[9]
Virus specifics
[edit]CIH spreads under the Portable Executable file format under the Windows 9x-based operating systems, Windows 95, 98, and ME. CIH does not spread under Windows NT-based operating systems nor Win16-based operating systems such as Windows 3.x or below.[10]
CIH infects Portable Executable files by splitting the bulk of its code into small slivers inserted into the inter-section gaps commonly seen in PE files and writing a small re-assembly routine and table of its own code segments' locations into unused space in the tail of the PE header. This earned CIH another name, "Spacefiller". The size of the virus is around 1 kilobyte, but due to its novel multiple-cavity infection method, infected files do not grow at all. It uses methods of jumping from processor ring 3 to 0 to hook system calls.
The payload, which is considered extremely dangerous, first involves the virus overwriting the first megabyte (1024KB) of the hard drive with zeroes, beginning at sector 0. This deletes the contents of the partition table, and may cause the machine to hang or cue the blue screen of death.
The second payload tries to write to the Flash BIOS. BIOSes that can be successfully written to by the virus have critical boot-time codes replaced with junk. This routine only works on some machines. Much emphasis has been put on machines with motherboards based on the Intel 430TX chipset, but by far the most important variable in CIH's success in writing to a machine's BIOS is the type of Flash ROM chip in the machine. Different Flash ROM chips (or chip families) have different write-enable routines specific to those chips. CIH makes no attempt to test for the Flash ROM type in its victim machines and has only one write-enable sequence.
For the first payload, any information that the virus has overwritten with zeros is lost. If the first partition is FAT32, and over about one gigabyte, all that will get overwritten is the MBR, the partition table, the boot sector of the first partition and the first copy of the FAT of the first partition. The MBR and boot sectors can simply be replaced with copies of the standard versions; the partition table can be rebuilt by scanning over the entire drive and the first copy of the FAT can be restored from the second copy. This means a complete recovery with no loss of user data can be performed automatically by a tool like Fix CIH.
If the first partition is not FAT32 or is smaller than 1 GB, the bulk of user data on that partition will still be intact, but without the root directory and FAT it will be difficult to find it, especially if there is significant fragmentation.
If the second payload executes successfully, the computer will not start at all. Reprogramming or replacement of the Flash BIOS chip is then required, as most systems that CIH can affect predate BIOS restoration features.
Variants
[edit]| Moniker | Description |
|---|---|
| CIH v1.2/CIH.1003 | This variant is the most common one and activates on April 26. It contains the string: CIH v1.2 TTIT |
| CIH v1.3/CIH.1010.A and CIH1010.B | This variant also activates on April 26. It contains the string: CIH v1.3 TTIT |
| CIH v1.4/CIH.1019 | This variant activates on the 26th of any month. It contains the string CIH v1.4 TATUNG. |
| CIH.1049 | This variant activates on August 2 instead of April 26. |
See also
[edit]References
[edit]- ^ a b "從CIH「重裝駭客」變身「除錯超人」". iThome online (in Chinese). 2006-08-25. Archived from the original on 2013-04-17.
- ^ a b c "從駭電腦到愛旅行─昔日網路小子陳盈豪 - 親子天下雜誌8期 - 陳盈豪,網路世界,宅男,網路沉迷". parenting.com.tw (in Chinese). 2013-06-07. Archived from the original on 2013-06-07.
- ^ "打擊駭客,不再無法可施 - 安全常識 - 法務部行政執行署嘉義分署" (in Chinese). 行政執行署嘉義行政執行處. 2005-12-10. Archived from the original on 2013-10-29.
{{cite web}}: CS1 maint: unfit URL (link) - ^ a b "What is the Chernobyl Virus? (with pictures)". Easy Tech Junkie. Retrieved 2023-02-16.
- ^ Weil, Nancy (1999-04-07). "Some Aptivas shipped with CIH virus". CNN. Archived from the original on 2007-01-04.
- ^ "Back Orifice CDs infected with CIH virus - Tech News on ZDNet". ZDNet. July 14, 1999. Archived from the original on 2007-03-11.
- ^ "US Report: Gamers believe Activision's 'SiN' carries CIH virus". ZDNet.co.uk. 28 Jul 1998. Archived from the original on 2009-04-17.
- ^ Lemos, Robert (May 25, 1999). "Is the CIH virus on the endangered list?".
- ^ "Virus:DOS/CIH". F-Secure Labs. Archived from the original on 2001-01-28. Retrieved 2021-12-07.
- ^ "Virus:DOS/CIH | F-Secure Labs". www.f-secure.com. Retrieved 2023-11-05.
External links
[edit]- F-Secure CIH Database
- F-Secure CIH Technical Page
- Symantec CIH Technical Page
- News article about the Jennifer Lopez e-mail
- FIX-CIH - Site by Steve Gibson on how to repair most of the damage from CIH
- CIH 1.4 source code
